Snowden’s revelations had put into evidence the seemingly strong link between new technologies such as the Internet and the capacity of some states to harness it as a tool for massive surveillance in real time. As some had argued, these revelations were not that shocking after all as they only confirmed what many have been discussing for a few years but had no real evidence in hand. Now they do.
 But is this link inherent to the new technologies? In other words, does the rapid development of new Information and Communication Technologies (ICTs) necessarily has a positive correlation with surveillance? By the way, these sort of questions also relates to the common notion out there that technologies are “neutral” by default. But we will deal with this issue on a later post.
But is this link inherent to the new technologies? In other words, does the rapid development of new Information and Communication Technologies (ICTs) necessarily has a positive correlation with surveillance? By the way, these sort of questions also relates to the common notion out there that technologies are “neutral” by default. But we will deal with this issue on a later post.
In any event, these are some of the questions that the latest book by Bruce Schneier wants to address.
In his view, new technologies and digital platforms provide fertile ground for massive data collection and tracking of individuals to the degree that was unimaginable before. The former East German Minister of State Security (aka Stasi) would have loved to have access to the new technologies. Fortunately, they did not. But, for a while, Stasi was very effective in achieving most of its sinister goals.
Being that as it may, the massive amounts of data collection and detailed tracking lays the basis for mass surveillance by both governments and the private sector. Shneier argues that we are partly responsible for this as we have indeed accepted at face value the trade-off between free access to the new technologies and platforms and their encroaching into our private lives. We need to revisit this “bargain,” especially if we are fully aware of the dangers of mass surveillance.
Shneier makes his case in three parts: 1. Depicting the breadth and depth of mass surveillance in today’s society. 2. Analyzing the harms that mass surveillance has in society; and 3. Making recommendations and suggestions on how to confront these challenges.
The ensuing of mass surveillance capabilities is the result of two overall trends. First, the declining costs of collecting massive amounts of data facilitated in significant measure by the emergence of new technologies that allow for personal tracking. Before this happened, surveillance was an expensive business as it required lots of (hu)manpower – going back to Stasi, they had one spy for every 166 East German citizens (pg. 23). Nowadays, computers and platforms can track us without any direct human intervention. “The result of this declining cost of surveillance technology is not just a difference in price; it’s a difference in kind” (pg. 26). For example, we have seen the emergence of private sector companies that collect data of all sorts and sell them for a profit. We also have “automatic surveillance” which allows tracking people who do not want to be tracked by tracking others who interact with them, etc. Indeed, it is not at all easy to escape the mass surveillance scenario in the current context.
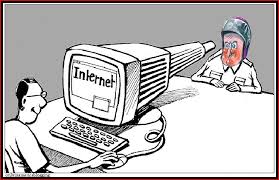
The second overall trend is the emergence of the Internet which has de facto created ONE network of networks that most people use, thus easily crossing national and regional borders without passports or visas. Nowadays, we are all connected to the same plug, so in principle, anyone with the right technologies and platforms can track and spy on us. Contrast this with older surveillance capabilities. At any rate, the critical point here is the emergence of “the public-private surveillance partnership” (pg. 80) which brings together government and the business sector to undertake mass surveillance. While the government piggybacks on the latter, the private sector has not been really forced to join such partnership (pg. 82). But governments can use legislation, install backdoors and pressure companies to help them spy on people.
second overall trend is the emergence of the Internet which has de facto created ONE network of networks that most people use, thus easily crossing national and regional borders without passports or visas. Nowadays, we are all connected to the same plug, so in principle, anyone with the right technologies and platforms can track and spy on us. Contrast this with older surveillance capabilities. At any rate, the critical point here is the emergence of “the public-private surveillance partnership” (pg. 80) which brings together government and the business sector to undertake mass surveillance. While the government piggybacks on the latter, the private sector has not been really forced to join such partnership (pg. 82). But governments can use legislation, install backdoors and pressure companies to help them spy on people.
In terms of the many harms that ubiquitous surveillance, Shneier includes: using data to prosecute people; censorship by government; intimidation of journalists and others; preventing dissent and social change; increased secrecy in government operations; abuse of power; restricting Internet Freedom; more discrimination and manipulation; privacy breaches; and a negative perception of the private sector (as a result of its “partnership” with government).
Two chapters in this section are dedicated to privacy and security respectively. For Shneier, “privacy is an inherent human right and a requirement for maintaining the human condition with dignity and respect. It is about choice, and having the power to control how you present yourself to the world.” (pg. 126). Nowadays, however, this is more difficult to sustain as almost everything we say and do is being digitally recorded by algorithms. And in this process, being anonymous becomes a daunting challenge.
The chapter on security focuses on the effectiveness of mass surveillance to prevent terrorist acts which face three core challenges: too many false positives; the uniqueness of most terrorist attacks; and, detection avoidance by terrorists themselves. Use of big data and data mining are not very effective when it comes to terrorism. It is more useful to eavesdrop on specific targets. Here, the widespread use of encryption can play a key role while fostering privacy at the same time. Equally important is the stockpiling of software vulnerabilities by governments who prefer to keep them private than to solve them. This can give them a temporary advantage vis-a-vis other competing or enemy nations but ends up making all of us much less secure. The same goes for encryption undermining, Internet hacking and use of hardware and software backdoors.
The last section presents concrete proposals for addressing most of these issues, organized by sector: government, business and end users. The chapter on Principles that opens this section provides the analytical framework for the subsequent analysis. Shneier reminds us that privacy and security are two sides of the same coin – and not opposites, as it is usually presented by governments, private companies, and the media. Also, security and surveillance are negatively correlated: “a system built for security is harder to surveil” (pg. 157). But security is always more important than surveillance. The other principles relate to governance principles: transparency, oversight, and accountability. A final one deals with “resilient design” (pg. 163) which can be used to address the inevitable imperfections inherent to system and institutional designs.
So how do we get out of this conundrum? Shnenier makes a couple of suggestions here (manage fear and privacy, act now) but seems to end with a big question: “how do we design systems that make use of our data collectively to benefit society as a whole, while at the same time protecting people individually?” (pg. 237). It will certainly not be easy to solve this question, and the author suggests that this will only happen in the long run term. But we are also invited to start taking matters into our own hands right away. Now!
So what are you waiting for?
Schneier, Bruce. 2015. Data and Goliath: The Hidden Battle to Collect Your Data and Control the World. New York: W. W. Norton & Co. ISBN: 978-0-393-24481-6.